In an increasingly interconnected yet heavily scrutinized digital world, the need for robust online security and privacy tools has never been more critical. Users worldwide grapple with issues ranging from pervasive surveillance and geo-restrictions to outright censorship and sophisticated network firewalls. While Virtual Private Networks (VPNs) have become a mainstream solution, a new generation of more specialized and often more resilient tools is emerging to tackle these challenges. Among these, DarkTunnel - SSH DNSTT V2Ray stands out as a powerful utility designed for users seeking advanced methods to secure their internet connection, bypass restrictions, and maintain anonymity.
DarkTunnel - SSH DNSTT V2Ray, available as a free utility application for Android, offers a sophisticated suite of networking tools centered around establishing an SSH tunnel server. It aims to provide a secure conduit for online activities, ensuring that internet traffic is encrypted and routed in a way that protects user data from prying eyes and allows access to an unfettered internet. Developed as a robust alternative for those who find traditional VPN services insufficient or inaccessible, DarkTunnel integrates multiple tunneling protocols and transport options to offer unparalleled flexibility and resilience against various network obstacles.
The application’s primary appeal lies in its multifaceted approach to online protection. By combining SSH tunneling with DNSTT (DNS Tunneling) and V2Ray protocols, DarkTunnel creates a formidable shield against censorship and surveillance. This combination allows users to circumvent stringent firewalls, access websites and services that are otherwise blocked in their region, and browse the web with an enhanced layer of anonymity. For many, it represents a crucial tool in the ongoing battle for digital freedom and privacy.
Understanding DarkTunnel’s Core Technologies: SSH, DNSTT, and V2Ray
To truly appreciate the capabilities of DarkTunnel - SSH DNSTT V2Ray, it’s essential to delve into the underlying technologies that power this robust application. Each component plays a vital role in creating a secure, flexible, and resilient tunneling solution.
SSH (Secure Shell) Tunneling: The Foundation of Security
At its heart, DarkTunnel leverages SSH, or Secure Shell. SSH is a cryptographic network protocol that enables secure data communication, remote command-line login, and other secure network services between two networked computers. While commonly used for secure remote access to servers, SSH’s tunneling capabilities are what DarkTunnel primarily exploits.
An SSH tunnel, often referred to as SSH port forwarding, creates a secure, encrypted connection between a local port and a remote port through an SSH server. All traffic routed through this tunnel is encrypted, shielding it from eavesdropping, man-in-the-middle attacks, and unauthorized inspection by Internet Service Providers (ISPs) or government agencies. When you use DarkTunnel with SSH, your entire internet connection can be encapsulated within this secure tunnel. This means that instead of your data flowing directly and openly from your device to its destination, it first travels securely to an SSH server, and from there, emerges onto the internet. This obfuscates your true IP address and encrypts your data, making it appear as if your traffic originates from the SSH server, thus enhancing both privacy and the ability to bypass network-level blocking.
The strength of SSH tunneling lies in its ubiquitous nature and its inherent encryption. Because SSH is a standard and often whitelisted protocol, traffic routed through an SSH tunnel can often bypass firewalls that block other VPN or proxy protocols. It’s a fundamental building block for secure communication in the digital realm, and DarkTunnel harnesses its power to create a reliable and private pathway for your online activities.
DNSTT (DNS Tunneling): Stealth Through the Backdoor
One of DarkTunnel’s more advanced features is its integration of DNSTT, which refers to DNS (Domain Name System) tunneling. DNS is a fundamental service that translates human-readable domain names (like phanmemfree.org) into machine-readable IP addresses. DNS queries are typically unencrypted and are often allowed through even the strictest firewalls because they are essential for basic internet functionality.
DNS tunneling exploits this characteristic by encapsulating other protocols’ data (like IP or HTTP traffic) within DNS queries and responses. Imagine sending secret messages hidden within seemingly innocuous requests for website addresses. This method is incredibly stealthy because DNS traffic is rarely inspected as rigorously as other forms of network traffic. For adversaries or network administrators, distinguishing legitimate DNS queries from those carrying tunneled data can be exceptionally difficult.
DarkTunnel’s use of DNSTT provides an extremely robust way to bypass internet censorship and highly restrictive network environments. When other tunneling methods might be detected and blocked, DNS tunneling can often slip through unnoticed, providing a lifeline for internet access. This is particularly valuable in regions with advanced censorship infrastructures that actively seek to identify and block VPNs and other traditional circumvention tools. However, DNS tunneling can be slower than other methods due to the nature of DNS queries and responses, which are not designed for high-bandwidth data transfer. Despite this, its effectiveness in extreme situations makes it an invaluable component of DarkTunnel’s arsenal.

V2Ray: The Advanced Proxy Platform
V2Ray is a powerful and versatile platform for building custom proxy networks. It is not a single protocol but rather a collection of tools and protocols designed to help users bypass network restrictions and enhance internet security. V2Ray offers a wide array of transport protocols, including VMess, VLESS, Trojan, Shadowsocks, and HTTP/2, along with various obfuscation techniques.
The integration of V2Ray into DarkTunnel significantly enhances its capabilities beyond simple SSH or DNS tunneling. V2Ray is known for its ability to disguise traffic to look like ordinary web traffic (e.g., HTTPS), making it very difficult for deep packet inspection (DPI) systems to detect and block. This obfuscation is crucial for combating sophisticated censorship mechanisms that can identify and block known VPN protocols.
V2Ray’s flexibility means it can be configured in numerous ways to adapt to different network conditions and censorship tactics. It supports features like Mux (multiplexing multiple connections over a single TCP connection for better performance), routing rules (to selectively route traffic), and various security features. By including V2Ray, DarkTunnel offers users a high degree of adaptability and resistance against even the most advanced forms of internet blocking. This makes DarkTunnel a formidable tool for those in highly censored environments, providing multiple layers of obfuscation and encryption that are hard to penetrate.
In summary, DarkTunnel’s strength lies in its ability to combine these three powerful technologies. SSH provides a secure and generally accepted encrypted channel. DNSTT offers a highly stealthy method for bypassing restrictions by leveraging essential network services. V2Ray brings advanced obfuscation, multiple protocols, and high flexibility to evade sophisticated detection systems. This multi-protocol approach makes DarkTunnel a versatile and resilient solution for securing online traffic and achieving digital freedom.
The Quest for Secure and Anonymous Browsing: DarkTunnel’s Approach
In an era where digital footprints are constantly tracked and online privacy is under increasing threat, DarkTunnel - SSH DNSTT V2Ray emerges as a crucial tool for users prioritizing secure and anonymous browsing. Its multifaceted approach directly addresses some of the most pressing concerns faced by internet users today: bypassing firewalls, combating censorship, and ensuring anonymity.
Bypassing Firewalls and Censorship
One of the most significant advantages of DarkTunnel is its ability to bypass stringent firewalls and overcome internet censorship. Many regions worldwide impose strict rules that restrict access to certain websites, social media platforms, news outlets, and online services. These restrictions can range from government-imposed blocks to institutional network policies (e.g., school or workplace networks).
DarkTunnel’s combination of SSH, DNSTT, and V2Ray protocols offers multiple avenues to circumvent these barriers.
- SSH’s Standard Port Usage: SSH commonly operates on port 22, a port that is typically open on most networks as it’s essential for remote administration. By routing traffic through an SSH tunnel, DarkTunnel can make your internet activity appear as standard SSH communication, often slipping past basic firewall rules that block other protocols.
- DNSTT’s Stealth: As discussed, DNS tunneling leverages DNS queries, a fundamental and rarely blocked internet service. This stealthy approach allows data to pass through even highly restrictive firewalls that employ deep packet inspection to identify and block common VPN protocols. It’s a “last resort” method that often succeeds when all else fails.
- V2Ray’s Obfuscation: V2Ray is designed with sophisticated obfuscation techniques that can mimic ordinary HTTPS traffic, making it incredibly difficult for automated censorship systems to detect. By making encrypted traffic look like regular web browsing, V2Ray effectively hides the fact that a user is employing a circumvention tool.
This layered approach means that DarkTunnel offers resilience against various types of blocking mechanisms, from simple port blocking to advanced protocol detection. For users in heavily censored countries, such as China, Iran, or parts of Russia, DarkTunnel can be an invaluable lifeline to the global internet, enabling access to information and communication tools that would otherwise be inaccessible.
Encrypted Online Traffic for Enhanced Security and Protection
Beyond bypassing restrictions, DarkTunnel’s core function is to encrypt online traffic, providing a critical layer of security and protection. Every piece of data transmitted over the internet, from browsing history to sensitive login credentials, is vulnerable to interception if not properly encrypted. Public Wi-Fi networks, in particular, are notorious for their security vulnerabilities, making users susceptible to eavesdropping and data theft.
DarkTunnel addresses this by encapsulating all user data within encrypted tunnels. Whether it’s an SSH tunnel, a V2Ray connection, or even data within a DNSTT stream, the information is scrambled and rendered unreadable to unauthorized parties. This encryption ensures:
- Data Confidentiality: Your browsing activities, emails, messages, and banking transactions remain private and cannot be intercepted and read by your ISP, government agencies, or malicious actors.
- Protection Against Eavesdropping: On unsecured networks, such as public Wi-Fi hotspots, your data is protected from those attempting to “sniff” network traffic.
- Integrity: Encryption also typically ensures the integrity of the data, meaning it cannot be tampered with in transit without detection.
This robust encryption is comparable to, and in some cases even more advanced than, what is offered by many commercial VPN services. For individuals concerned about their digital security posture, DarkTunnel provides peace of mind that their online communications are protected from pervasive surveillance and cyber threats.
Anonymity for Improved Privacy While Online
Anonymity is a cornerstone of online privacy, allowing users to browse the internet without revealing their true identity or location. DarkTunnel significantly enhances user anonymity by masking the originating IP address.
When you connect through DarkTunnel, your internet traffic first passes through the designated SSH or V2Ray server. To the websites and services you access, your connection appears to originate from the server’s IP address, not your actual device’s IP address. This effectively hides your real geographical location and makes it much harder for third parties to track your online activities back to you.
The benefits of this enhanced anonymity include:
- Reduced Tracking: Advertisers, data brokers, and websites find it harder to build detailed profiles of your online behavior linked to your identity.
- Freedom of Expression: In environments where speaking freely online might have repercussions, anonymity provides a shield, allowing individuals to express themselves without fear of reprisal.
- Protection from Targeted Attacks: Hiding your IP address makes you a less accessible target for direct cyberattacks.
While no tool can guarantee absolute anonymity, DarkTunnel’s sophisticated tunneling and obfuscation techniques significantly raise the bar, making it much more challenging for entities to link online actions back to individual users. This combination of firewall circumvention, strong encryption, and IP masking positions DarkTunnel as a powerful ally in the ongoing quest for a more secure and private internet experience.
Key Features and Configuration Options of DarkTunnel
DarkTunnel - SSH DNSTT V2Ray is distinguished by its extensive array of features and highly customizable configuration options, designed to cater to a diverse range of networking needs and to adapt to varying network conditions. This flexibility is what makes it a potent tool for bypassing restrictions and securing online traffic.
The application offers several critical parameters that users can adjust to fine-tune their connection:
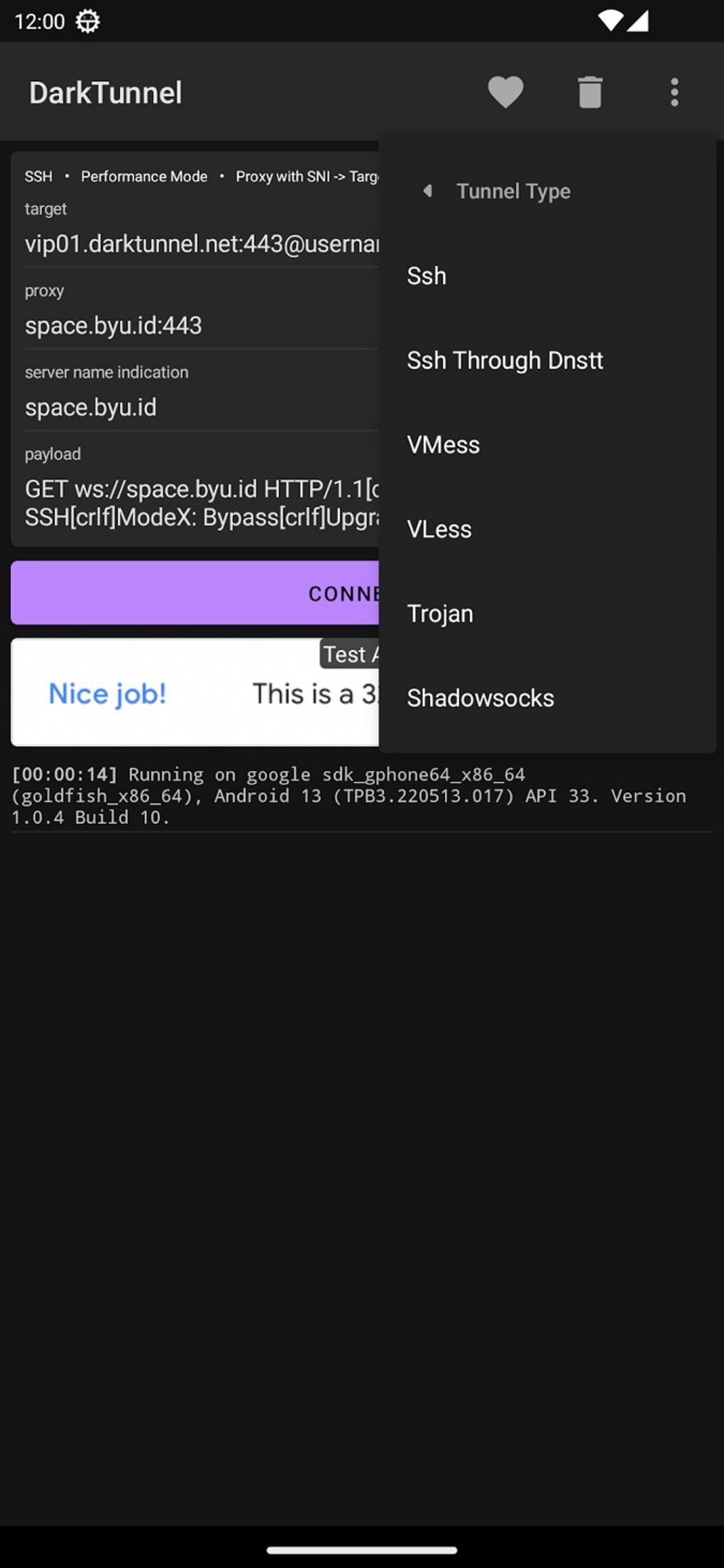
Seven Tunnel Types to Choose From
DarkTunnel provides users with a selection of “seven tunnel types,” which likely refer to different primary protocols or combinations of protocols that the application can initiate. While the exact nomenclature within the app isn’t explicitly detailed in the reference, these typically represent different approaches to establishing a secure connection:
- Direct SSH: A straightforward SSH tunnel, where traffic is directly encapsulated within the SSH protocol.
- SSH + HTTP Proxy: Combines SSH with an HTTP proxy layer, often useful for web browsing and bypassing HTTP-specific restrictions.
- SSH + SSL/TLS: Encapsulates SSH traffic within SSL/TLS, making it appear as secure web traffic (HTTPS), which is highly effective against firewalls that inspect traffic signatures.
- DNSTT Tunnel: Utilizes DNS tunneling as the primary method for data transmission, ideal for highly restricted networks where other protocols are blocked.
- V2Ray (VMess/VLESS/Trojan): Employs V2Ray’s advanced protocols with their inherent obfuscation capabilities, designed to mimic regular internet traffic.
- WebSocket + TLS: Routes traffic over WebSockets, which can then be further protected by TLS, often used for bypassing firewalls that allow WebSocket connections.
- Custom Payload/Injector: Allows advanced users to craft custom request headers or payloads, providing an additional layer of obfuscation and making it extremely difficult for network systems to identify and block the connection.
This variety empowers users to experiment and find the most effective tunnel type for their specific network environment, adapting to different levels of censorship and network restrictions.
Three Transport Network Options
In addition to the primary tunnel types, DarkTunnel offers “three transport network options.” These refer to the underlying methods by which the encrypted data is carried across the internet. Different transport options can offer varying degrees of stealth, speed, and resilience. Common transport options include:
- TCP (Transmission Control Protocol): The most common internet transport protocol, reliable and connection-oriented. While widely used, TCP traffic patterns can sometimes be identifiable.
- UDP (User Datagram Protocol): A connectionless protocol, often faster for real-time applications but less reliable. UDP is increasingly used for tunneling and can sometimes bypass restrictions where TCP is blocked.
- ICMP (Internet Control Message Protocol): Typically used for diagnostic purposes (like ping), ICMP tunneling is a highly stealthy method, similar to DNS tunneling, for encapsulating data. It’s often used as a “covert” channel.
The ability to switch between these transport options provides an extra layer of adaptability. For instance, if TCP-based tunneling is being actively throttled or blocked, switching to a UDP or even ICMP-based transport could maintain a connection.
Five Inject Modes Available
DarkTunnel also boasts “five inject modes,” which likely relate to how data is initially injected or modified at the client side before entering the tunnel. These modes are crucial for obfuscating the initial handshake or the appearance of the traffic to make it look innocuous. Inject modes can include:
- Normal Inject: Standard injection without specific obfuscation.
- Front Inject: Inserts the tunnel header at the beginning of an HTTP request, making it look like a standard web request.
- Back Inject: Places the tunnel header at the end of an HTTP request.
- Query Inject: Embeds the tunnel data within the query string of an HTTP request.
- Payload Inject: Allows for injecting custom payloads or HTTP headers to mimic specific, legitimate traffic patterns, thereby bypassing content-aware firewalls.
These inject modes are particularly useful in environments where network administrators employ deep packet inspection (DPI) to identify and block unusual or non-standard traffic. By mimicking legitimate HTTP or other protocol requests, DarkTunnel can trick DPI systems into allowing the tunneled traffic to pass through.
The Power of Customization and User Control
The combination of these multiple tunnel types, transport options, and inject modes gives DarkTunnel a significant edge in environments with sophisticated censorship. It essentially provides a toolkit for advanced users to craft a highly customized and adaptive connection profile. Unlike many simpler VPN applications, DarkTunnel requires a degree of technical understanding and willingness to experiment, but in return, it offers a level of control and resilience that few others can match.
This extensive configurability means that even if one method becomes compromised or blocked, users have numerous other combinations to try. It empowers individuals to take charge of their online security and privacy, providing them with the means to stay connected and secure regardless of the obstacles they face. While this level of customization might seem daunting to a novice, for those seeking robust circumvention, it is precisely what makes DarkTunnel an exceptionally valuable utility.
Navigating the Landscape of Online Privacy: DarkTunnel vs. VPNs
In the quest for online privacy, security, and unrestricted internet access, users are often presented with a dilemma: choose a traditional Virtual Private Network (VPN) or opt for more specialized tools like DarkTunnel - SSH DNSTT V2Ray. While both serve the overarching goal of securing internet traffic and bypassing restrictions, their mechanisms, target audiences, and effectiveness in various scenarios differ significantly. DarkTunnel positions itself as a robust “decent option” for those seeking the benefits of VPN services without typical VPN constraints.
Traditional VPNs: The Mainstream Choice
VPNs have become a household name, offering an accessible and generally user-friendly solution for online privacy.
- Simplicity: Most commercial VPNs provide dedicated apps that allow users to connect with a single tap, selecting from a vast network of servers worldwide.
- Global Reach: They typically offer thousands of servers in numerous countries, enabling users to easily access geo-restricted content from almost any region.
- Established Security: VPNs use well-understood tunneling protocols (like OpenVPN, WireGuard, IKEv2) to encrypt traffic between the user’s device and the VPN server.
- Subscription Model: The majority of reliable VPN services operate on a subscription basis, which funds their infrastructure and continuous development.
However, VPNs also face challenges, particularly in highly censored environments:
- Detectability: Many VPN protocols can be identified and blocked by advanced firewalls that use deep packet inspection (DPI).
- Cost: The subscription model, while beneficial for ongoing service, can be a barrier for some users or in regions with economic hardship.
- Trust: Users must place significant trust in the VPN provider regarding their no-logs policy and overall security practices.
DarkTunnel: A Specialized Alternative
DarkTunnel - SSH DNSTT V2Ray steps in as a specialized alternative, particularly appealing to users who encounter limitations with traditional VPNs or prefer a more hands-on approach.
- Advanced Evasion Capabilities: DarkTunnel’s strength lies in its multi-protocol approach (SSH, DNSTT, V2Ray) and extensive configuration options (tunnel types, transport modes, inject modes). These features are specifically designed to bypass even the most sophisticated firewalls and censorship systems that successfully block conventional VPN traffic. DNSTT, in particular, offers a level of stealth rarely found in commercial VPNs.
- Cost-Effectiveness (Often Free): DarkTunnel itself is a free application. While users might need access to an SSH or V2Ray server (which can be self-hosted or obtained from various providers, some free, some paid), the core application doesn’t require a subscription. This makes it an attractive option for users unwilling or unable to pay for a VPN subscription.
- Greater Control and Customization: DarkTunnel offers unparalleled control over how the connection is established and disguised. This is ideal for technical users who want to fine-tune their settings for optimal performance and stealth in specific network environments.
- Less Prone to Mass Blocking: Because its methods are more obscure and customizable, DarkTunnel connections are often harder to identify and block en masse compared to well-known VPN protocols.
When to Choose Which?
- Choose a VPN if: You prioritize ease of use, require access to a wide variety of global server locations, are willing to pay for a subscription, and are not operating under extremely restrictive network conditions where common VPN protocols are heavily blocked. Most casual users and those in less censored regions will find a VPN perfectly adequate.
- Choose DarkTunnel if: You are in a heavily censored region where traditional VPNs are consistently blocked, you possess technical knowledge and enjoy customizing network settings, you need a free or low-cost solution, or you prioritize the most advanced obfuscation and evasion techniques. It’s particularly suited for power users, activists, or individuals in highly surveilled environments.
The “Decent Option” Verdict
PhanMemFree’s assessment of DarkTunnel as “a decent option” accurately captures its value. It offers the “security and privacy benefits of VPN services” – namely, encrypted traffic, IP masking, and circumvention – but through a different, often more resilient, technical pathway. The key trade-off for this enhanced resilience and customizability is typically a steeper learning curve and potentially less stable connections compared to a well-maintained commercial VPN service.
For users who are constantly battling network restrictions and finding themselves unable to connect with conventional VPNs, DarkTunnel provides a powerful, often indispensable, alternative. It represents a niche but critical solution in the diverse landscape of online freedom tools, empowering users with the advanced capabilities needed to navigate a complex and often restrictive digital world.
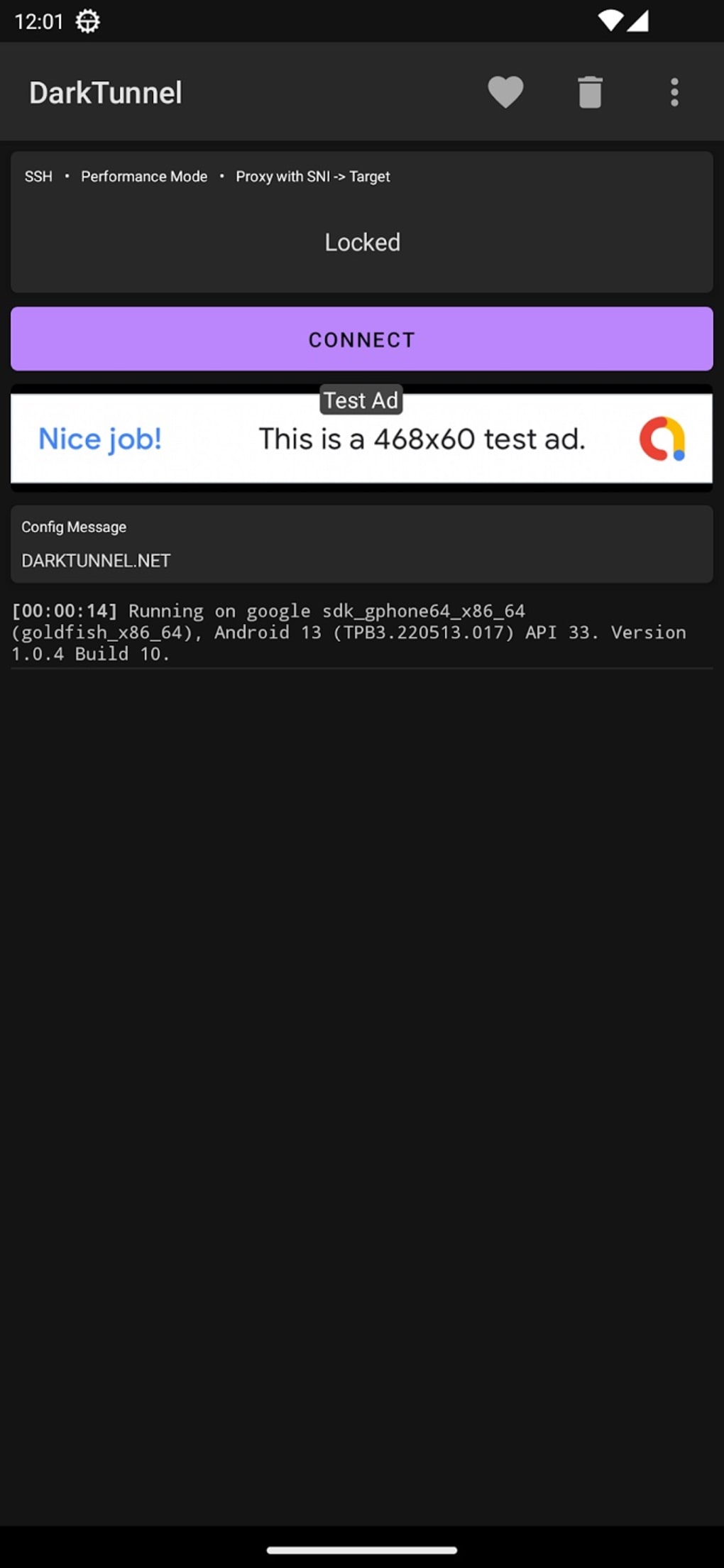
Performance, Stability, and User Experience: A Balanced View
When evaluating a utility like DarkTunnel - SSH DNSTT V2Ray, it’s crucial to consider not just its feature set and technical prowess, but also its real-world performance, connection stability, and overall user experience. While DarkTunnel offers a robust suite of tools for enhanced security and privacy, the PhanMemFree review highlights a significant aspect that warrants a balanced perspective: “connection stability is inconsistent and erratic at times.”
The Double-Edged Sword of Advanced Obfuscation
DarkTunnel’s strength, its highly customizable and obfuscated tunneling methods, can also be its Achilles’ heel concerning stability. The very techniques that make it effective in bypassing restrictions—such as encapsulating traffic within DNS queries or mimicking HTTPS—are often resource-intensive or rely on less conventional network pathways.
- DNSTT (DNS Tunneling): While exceptionally stealthy, DNS tunneling is inherently slower and can be less stable than direct TCP/UDP connections. DNS is designed for small, rapid queries, not sustained high-bandwidth data transfer. This means that a connection relying heavily on DNSTT might experience higher latency and lower throughput, leading to a perception of “erratic” performance, especially for streaming or large downloads.
- V2Ray and Custom Payloads: While V2Ray offers excellent performance with proper configuration, misconfigurations or attempting to mimic traffic too aggressively can sometimes lead to connection drops or unstable speeds. Custom payloads and inject modes, while powerful, also add layers of complexity that can introduce instability if not precisely tuned for the network environment.
- Server Quality: The stability of DarkTunnel’s connection is heavily dependent on the quality and stability of the SSH or V2Ray server that the user connects to. If the remote server is overloaded, poorly maintained, or experiences network issues, the client-side connection will naturally suffer. Unlike commercial VPNs that manage their server infrastructure, DarkTunnel users might be relying on third-party servers or self-hosted instances, whose reliability varies greatly.
“Inconsistent and Erratic” Stability Explained
The phrase “inconsistent and erratic” likely refers to several common issues experienced by users:
- Frequent Disconnections: The tunnel might drop unexpectedly, requiring manual reconnection. This can be disruptive for activities requiring a persistent connection.
- Varying Speeds: Speeds might fluctuate wildly, ranging from fast to very slow, making it difficult to predict performance for bandwidth-intensive tasks.
- High Latency: Ping times might be high and inconsistent, affecting real-time applications like online gaming or voice/video calls.
- Difficulty Establishing Connection: Sometimes, the tunnel might fail to establish at all, requiring multiple attempts or changes in configuration.
These issues are not uncommon for advanced circumvention tools, especially those that rely on “covert” channels or complex obfuscation. They are often the price of admission for bypassing the most sophisticated firewalls.
“Works Well Enough for Day-to-Day Use”
Despite the stability concerns, the PhanMemFree review concludes that “things are working well” and it “works well enough for day-to-day use.” This seemingly contradictory statement suggests a balanced reality:
- Resilience vs. Perfection: While not perfectly stable, DarkTunnel’s ability to provide any internet access in highly restricted environments makes its occasional instability a manageable trade-off. For many users, having intermittent access is infinitely better than no access at all.
- Context of Use: For activities like basic web browsing, checking emails, or sending messages, occasional drops or slower speeds might be tolerable. If the primary goal is simply to break through censorship, then DarkTunnel succeeds.
- User Adaptability: Experienced users might learn to work around the instabilities by switching tunnel types, transport options, or even changing remote servers. They understand that such tools require more active management than a typical VPN.
- Specific Configurations: Certain configurations might be more stable than others. A direct SSH tunnel might be more reliable than a DNSTT tunnel, depending on the network conditions. Users can experiment to find their sweet spot.
User Experience Considerations
- Technical Knowledge Required: DarkTunnel is not a plug-and-play solution. Its multiple configuration options, while powerful, necessitate a good understanding of networking concepts and patience for trial and error. This can be a significant barrier for novice users.
- Interface Complexity: While functional, the user interface might be more geared towards functionality and configuration depth rather than extreme simplicity or aesthetic polish, which is common for such utility apps.
- Community Support: Given its specialized nature, support might primarily come from online communities or forums rather than dedicated customer service, requiring users to be proactive in troubleshooting.
In conclusion, DarkTunnel - SSH DNSTT V2Ray presents a nuanced picture of performance and stability. It offers cutting-edge circumvention capabilities crucial for those in restricted environments, making it a valuable tool. However, users should anticipate that these advanced techniques might come with compromises in terms of consistent speed and unwavering connection stability compared to simpler, less-obfuscated solutions. For its target audience—users battling severe censorship and requiring advanced customization—its effectiveness in providing access often outweighs these performance caveats, making it indeed a “decent option” for securing online activities and maintaining digital freedom.
In the ever-evolving landscape of online security, DarkTunnel - SSH DNSTT V2Ray represents a powerful and flexible solution for a specific demographic: users who face stringent internet censorship, seek advanced privacy measures beyond typical VPNs, and are comfortable with a more technical approach. Its integration of SSH, DNSTT, and V2Ray protocols provides a versatile toolkit for bypassing firewalls, encrypting traffic, and enhancing anonymity.
While the application offers impressive configurability with its seven tunnel types, three transport network options, and five inject modes, this power comes with a steeper learning curve and, as noted, potential inconsistencies in connection stability. However, for those navigating highly restricted digital environments, the ability to establish a connection, even an erratic one, can be invaluable. It offers a free and highly customizable alternative to commercial VPNs, making advanced online security accessible to a broader audience.
Ultimately, DarkTunnel - SSH DNSTT V2Ray stands as a testament to the ongoing innovation in digital freedom tools. It empowers users to reclaim control over their internet experience, providing a robust shield against surveillance and censorship. For the technically inclined and those desperately seeking an open internet, DarkTunnel is more than just an app; it’s a vital pathway to freedom in the digital realm.
File Information
- License: “Free”
- Latest update: “July 12, 2025”
- Platform: “Android”
- OS: “Android 13.0”
- Language: “English”
- Downloads: “24.7K”
- Download Options: “Google Play”
















